Ethical Hacking

In a world where digital threats are growing more sophisticated every day, cybersecurity has become a top priority for businesses, governments, and individuals. One of the most crucial defenders in this digital age is the ethical hacker. Unlike malicious hackers who aim to steal, damage, or disrupt, ethical hackers—often called white hat hackers—use their skills to protect systems by identifying and fixing vulnerabilities before they can be exploited.
🔐 What is Ethical Hacking?

Ethical hacking is the authorized, legal practice of probing computer systems, networks, or applications to uncover security weaknesses. These experts simulate real-world cyberattacks but with a noble mission: to improve the security landscape of the organizations they work with.
They apply the same tools and techniques used by cybercriminals—but they do so with permission, full transparency, and ethical intent.
💡 Key Aspects of Ethical Hacking

✅ Authorization
Ethical hacking is never done without permission. The system or network owner must provide explicit consent, making the activity legal and legitimate.
🔍 Vulnerability Identification
The core objective is to discover flaws and weaknesses—loopholes that could be exploited by a malicious attacker.
🛠️ Remediation
Once vulnerabilities are found, ethical hackers help implement strategies, patches, and upgrades to secure the system.
⚖️ Legal and Ethical
Ethical hacking adheres to legal boundaries and moral responsibilities, aiming to protect rather than to harm.
💼 Career Path
Ethical hacking is one of the fastest-growing careers in the cybersecurity domain. It includes roles like penetration tester, security analyst, and cybersecurity consultant—with great demand across industries.
🔄 How Ethical Hacking Works: Step-by-Step Process
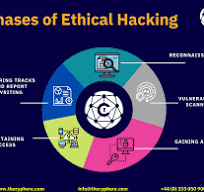
Ethical hackers follow a systematic approach to simulate an attack and assess an organization’s security posture:
1️⃣ Planning and Reconnaissance
The process begins with information gathering. Ethical hackers study the target system’s structure, networks, and applications to understand the landscape.
2️⃣ Vulnerability Scanning
Using specialized automated tools and manual testing methods, they scan for known security flaws or configuration errors.
3️⃣ Exploitation (with permission)
With prior approval, they attempt to exploit these vulnerabilities in a controlled environment to determine their impact.
4️⃣ Reporting and Remediation
After the testing phase, they prepare a comprehensive report detailing each vulnerability, its potential risks, and recommended fixes.
5️⃣ Covering Tracks
Just like real hackers, ethical hackers demonstrate how intruders could hide their presence—so organizations understand the importance of thorough threat monitoring.
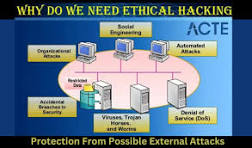
🎯 Why Ethical Hacking Matters Today

- 📊 According to industry reports, cyberattacks cost the global economy over $10 trillion annually.
- 🏛️ Governments and Fortune 500 companies rely on ethical hackers to guard sensitive data and prevent breaches.
- 👨💻 Small businesses are equally vulnerable—ethical hacking offers them a proactive defense strategy.
📽️ Learn More: How to Become an Ethical Hacker
Watch this short video from The Cyber Mentor to learn how to start your journey in ethical hacking:
👉 Watch on YouTube – 55 seconds
(Uploaded on Oct 29, 2024)
🚀 Conclusion
Ethical hacking is more than just a job—it’s a digital mission to protect the integrity of our interconnected world. By thinking like hackers—but acting as guardians—ethical hackers ensure that technology remains a tool for progress, not a weapon for exploitation.
If you’re curious about cybersecurity and want a career filled with challenge, impact, and growth—ethical hacking might just be your calling.
#Cybersecurity #EthicalHacking #WhiteHatHackers #InfoSec #HackingForGood


https://thenews.blogmirror.in